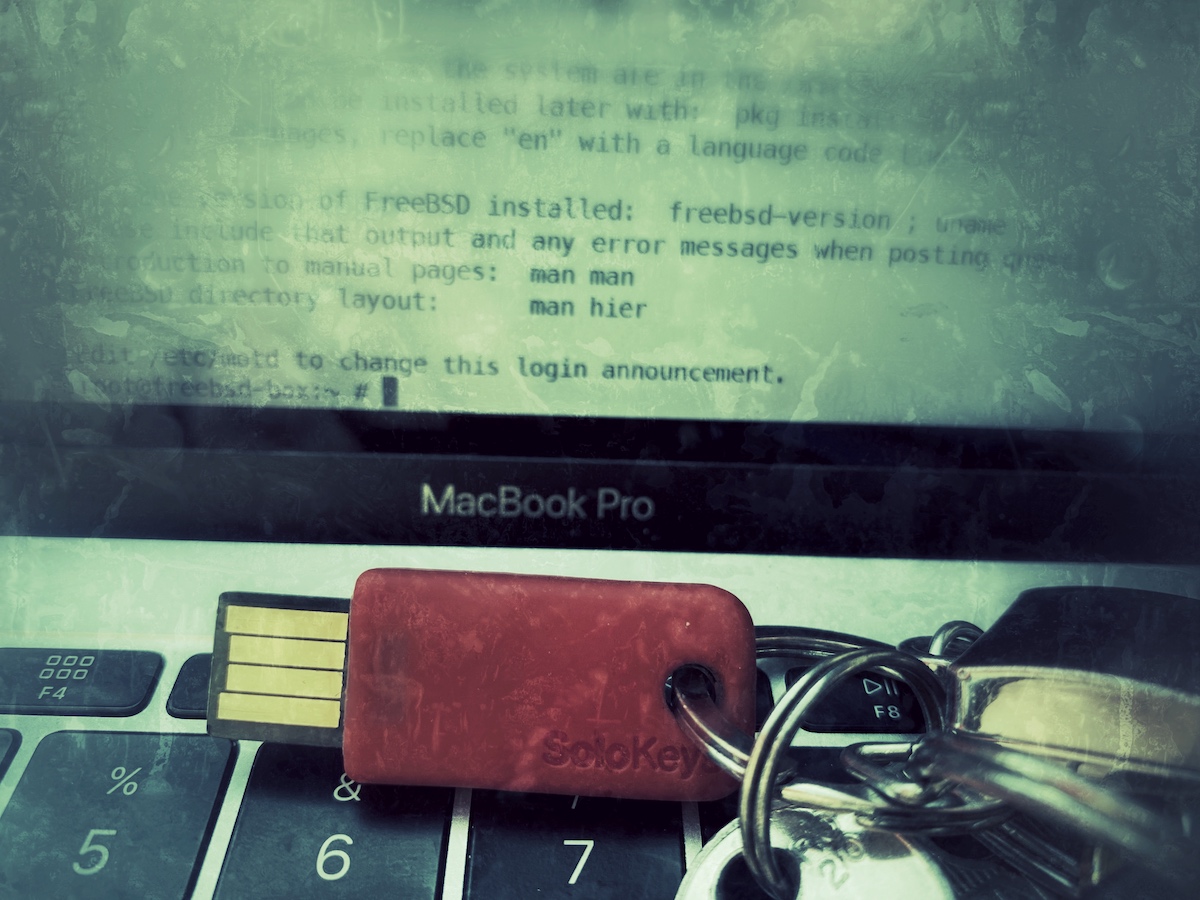
Using FIDO2 Auth Keys (Yubikey, Solokeys) with MacOS and FreeBSD
OpenSSH 8.2p1 with FIDO2 support was recently added to MacOS (via Homebrew) and FreeBSD (via ports/pkg).
Here’s a short how-to securely login to your FreeBSD servers via FIDO2 (Yubikey, Solokey et. al.).
On your MacOS client:
Open a terminal and install libfido2 and openssh (8.2p1)
brew install openssh libfido2
Generate you ecdsa key with libfido2.
Insert your FIDO2 usb stick and run (push the auth button on your key when prompted):
ssh-keygen -t ecdsa-sk
You may need to touch your authenticator to authorize key generation.
Enter file in which to save the key (/Users/username/.ssh/id_ecdsa_sk): /Users/username/.ssh/id_ecdsa_sk
Enter passphrase (empty for no passphrase): ############
Enter same passphrase again: ############
Your identification has been saved in /Users/username/.ssh/id_ecdsa_sk
Your public key has been saved in /Users/username/.ssh/id_ecdsa_sk.pub
cat ~/.ssh/id_ecdsa_sk.pub
and copy the key to your clipboard
[email protected] AAAAInNrLVk[...]ao8H== username@macos
On your FreeBSD box:
vim ~/.ssh/authorized_keys
and add your sk-ecdsa key.
install OpenSSH portable 8.2p1
portsnap fetch extract
make install -C /usr/ports/security/openssh-portable/
An alternative is switching from quartely to latest in /etc/pkg/FreeBSD.conf and run pkg install openssh-portable
To avoid locking out of your FreeBSD box you should run OpenSSH portable on a seperate port.
vim /usr/local/etc/ssh/sshd_config
Port 11022
#AddressFamily any
#ListenAddress 0.0.0.0
#ListenAddress ::
enable your portable SSH server:
sysrc openssh_enable=YES
service openssh start
Make sure you add the temporary SSH port to your pf.conf:
vim /etc/pf.conf
pass in on $inet_if inet proto tcp to $inet_ip port 10022
service pf reload
Finally:
Login to your server with your new Authkey.
Enter your passphrase and push button on your key.
ssh -p 11022 -i ~/.ssh/id_ecdsa_sk.pub user@hostname
Enter passphrase for key '.ssh/id_ecdsa_key':
Confirm user presence for key [...]
user@freebsd-box:~ #